Sunday, June 30, 2024
VPN Myth vs. Reality
Monday, May 6, 2024
Disable third-party cookie
Ideally, I’d like to block facebook.com here all together (i.e. disable it like I did with public.cobrowse.oraclecloud.com). However, it is not very practical because if I do that, I need login & authenticate to facebook.com every single time which is painful, so I let it be there at least I know they are not going to learn my banking activity for sure which is good enough.
Finally on a related cookie topic, I learned an interesting fact from a tech podcast with Steve Gibson (grc.com) on the annoying cookie permission pop-ups (GDPR compliance) we see on every website these days. It turns out that about 65% of the websites ignore what you choose and place tracking cookies anyway. You can view/hear the relevant section of the podcast here and here.
Tuesday, April 2, 2024
Free 1TB cloud storage?
Who says there is no free lunch? I saw this ad from TeraBox (terabox.com) for a free/permanent 1TB cloud storage which I thought was too good to be true. So, I created a free account and attempted to upload a huge 32GB file, but it failed saying for free tier, the largest file you are allowed to upload is 4GB. Ok fair enough, so I chopped the files into 4GB pieces and tried again. To my surprise, the free tier account uploaded all of them without any issue (see screenshot below), but it took longer since they do throttle upload speed for free tier which is totally understandable.
Thursday, January 18, 2024
Is your computer compromised?
Easy way to check if your computer is/was compromised now or in the past
With the recent addition of Naz.API dataset (a massive collection of over 1 billion stolen username and passwords) to HIBP service ("Have I Been Pwned" - a service by troyhunt.com), it is now very easy to check if your computer is compromised by information stealing malware now or in the past.
Go to the HIBP service at https://haveibeenpwned.com and enter your e-mail (don’t worry, it is 100% safe) and check the search results. The results may span several pages, so make sure to scroll down and check all the breaches your email is listed as compromised. Keep in mind that it is not at all unusual to see your email show up on multiple breaches. For example, see the screenshot below of my own email search.
Wednesday, January 3, 2024
New Year, New Password!
- Change your passwords (also change username if permitted)
- Enable password-less logins if available.
- If you don’t have 2F enabled, make sure to enable it.
- If the site supports stronger 2-factor mechanisms, like Authenticator app or better yet hardware key based, use that instead of SMS based 2-factor; While SMS based is better than just password alone, it is prone to attacks like SIM swap scams
- Validate your recovery mechanisms.
- Reset recovery app keys (if any)
- Validate recovery e-mail.
- Reset onetime login codes.
- Last but not least, invalidate all logins (i.e. log out from all devices and log back in). Though this step may be enforced by the password change, some sites don’t enforce it.
Wednesday, July 12, 2023
T-Mobile SIM swap protection
Many of us know or heard about how easy it is for cyber criminals to circumvent the SMS based 2FA authentication. While SIM swap scams are around for a while but according to FBI, it is currently on the rise. Ideally, you should use the authenticator app or better yet, hardware keys for 2FA but if the website only offers SMS based 2FA you have no choice but to use that. Unfortunately, lot of websites including some financial/banking websites offer only SMS based 2FA. If you are a T-Mobile customer, you can secure your SMS based authentication slightly better with T-Mobile SIM swap protection feature. I don’t know how well it actually protects but it is better than nothing. Log into your T-Mobile account and navigate to Account/Profile/Privacy & Notification/SIM protection to toggle it on as shown on the screenshot below. For convenience, the link below will take you to this setting directly if you are already logged into your T-Mobile account.
https://www.t-mobile.com/account/profile/fraud-block/simswap
Related Link:
https://www.wirefly.com/news/fcc-proposes-new-rules-stop-sim-swap-attacks
Stay Informed and Safe Online
Saturday, July 1, 2023
Three Simple Online Banking Safety Tips
Here are three simple steps you can take while doing online banking to minimize your chances of becoming a victim. As the title says, these steps are simple and does not take much time or effort to follow.
- Before login to your banking website for financial transactions or to even review your bank statement etc., close all tabs in your browser. If you are paranoid, temporarily disable any browser plugins you may have installed which you can turn on later.
- When you are logged into your banking website, do not do anything else like google search, Facebook, Instagram, or any other browsing specifically, read emails or worse, click on a link your buddy sent you to "check it out". You can do all that after step#3 below.
- Once you are done with your online banking business, make sure to log off. Many secure banking web sites these days do protect you by logging you off automatically. However, don’t rely on them because there are still some stupid online banking web sites that don’t properly log you out in a reasonable time or worse, don't do anything.
Simple Cyber Hygiene Practice
Here is some advice on simple cyber hygiene practices to protect yourself online. You really don't have to take extreme steps to bulletproof your online accounts because if a persistent and determined cyber criminals decided to target you (i.e., spear phishing), there is very little you can do to stop them especially if you are a high value target. Luckily most of us don't fall into that category unless you are dumb enough to divulge your personal info by posting on social media that makes you a target. However, with a bit of effort on your part, you can make it slightly harder for cybercriminals to scam you so they will move on to easy targets.
Friday, June 2, 2023
Facebook knows you way more than you think!
We all know that Facebook collects data on all of us. They manage to do that with different ways including via 3rd-party web browser cookies; an explanation of 3rd-party cookies goes beyond the scope of this blog but you can read about it here if you are interested to know more. While 3rd-party cookies are slowly phased out, the alternative i.e. FLoC proposed by Google, as per many privacy advocates, is even worse ... so for now, just assume Facebook and other platforms will always have a way to spy on you.
While there are ways to restrict what Facebook collects (follow steps at end of this blog), there is not a whole lot you can do to make them stop other than just deleting your Facebook account. The reason is, Facebook generates substantially all of its revenue by selling ads, so they have to monitor your online activity to slap you with targeted ads and curated content based on your web browsing behavior i.e., the sites you visit, shop, like etc. At the end of the day, Facebook knowing that I have T-Mobile wireless, or shop at Amazon or browse Reddit etc, is not a big deal for me, I just don't care. However, when I looked at what websites are sharing with Facebook, specifically, financial institution that I do business with, I was very concerned. My financial institution (will not mention their name here) shared with Facebook something related to my activity which is scarry, see below ...
It is unclear to me what they shared since I don't have the details other than Facebook telling me they did. I have the habit of clearing all cookies on banking and financial websites frequently, so unfortunately, I can no longer access this specific cookie in my browser to see the content of what all was shared with Facebook! However, based on the name of activity shared i.e., "COMPLETE_REGISTRATION", I can only assume it is not something I would like them to share, whatever it is. If it was just "PAGE_VIEW" like all other sites, I would be ok with it even then, why would Facebook need to know what bank website I visit? The only thing I remember is opening a new account, transferring money on those 2 days at that exact time mentioned which caused my concern. Why on earth Facebook needs this information? Just to give some perspective, this is just one specific instance of a website I have discussed above, there could be crap ton of them we visit every day sharing all kinds of stuff w/ Facebook 😮.
Finally, if you got this far, you could follow the steps below to tell Facebook to quit doing this, at least for now, until they figure out new ways of profiting on you 😃
Update: (May 22, 2024): Since many page links and interfaces have changed since this original post back in June 2022, I updated the details below as of today.
While logged in Facebook ...
- Navigate to https://www.facebook.com/off_facebook_activity
- Click "Manage future activity"
- Click on "Disconnect future activity.”
This will also clear all the stored activity, so you don't need to clear that. For visual reference, The screenshots for steps 2 and 3 are below.
Android Battery Drain
If your android phone runs out of battery sooner than you expected, you are not alone. The culprits are power hungry, and poorly designed smartphone apps you may have installed – trust me, there are lot of them including popular apps many of us use on a daily basis. To give an example, “Withings Health Mate” app that I use tracks weight from Withings Digital Scale and for some reason it adds a background task to sync the weight from the scale to cloud continually. This is insane ... why on earth anyone needs their weight to continually sync to cloud? A better design would be to sync to cloud whenever you open the app to check your weight history; there is absolutely no need to sync body weight continually especially it involves using your precious battery power. To make matters worse, some of them go totally nuts and do some crazy stuff. See my findings on fitbit at the link https://link.selvansoft.com/crazy-fitbit
Anyways, here is the list of top 10 apps that drain battery a lot.
- Fitbit
- Uber
- Skype
- Airbnb
- Tinder
- Bumble
- Snapchat
In my opinion, any phone can and should last a full day with heavy usage and two days on normal usage without having charge but if you have one or more of these installed, it is highly unlikely your phone battery will last all day long.
Solution:
The good news is, there is a way to limit the use of battery and extend your phones ability to last a whole day or two. For example, my phone battery lasts 2 full days on regular use. If you happened to run one of these apps above, just follow the video at link below to adjust the settings and enjoy longer battery charge!
https://selvansoft.com/public/videos/battery_optimize.mp4
Note: Some apps may not function properly while running in the background with this change, but most apps should work just fine. If you have any of them installed, just open each of them once so they will be listed on the recent list so you can easily find them, otherwise just search all the installed apps to find them to change the setting.
Finally, if you rarely use any of these power hogs, just uninstall them and install it back when you find the need to use. Another option is to enable “Google Play Instant” to run apps w/ out installing (note: Not all apps support this function). Go to your Google Play Store app Settings/General/Google Play Instant and enable it as shown in the screenshot.
Thursday, May 25, 2023
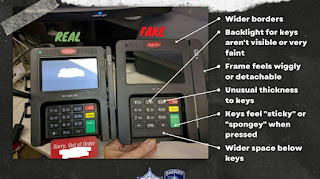
How to protect yourself from Card Skimmers
Before I go into steps to protect yourself from card skimmers, it is important to understand the various protocols used in POS (point of sale) devices to read your credit/debit cards. There are 4 types and they are --- swipe (magnetic strip), chip (chip in card), tap (RFID) and smartphone (NFC). I won’t go into the details on each of these, but it is sufficient to be aware that there are multiple technologies involved in POS transactions. Now, here are different ways to prevent or at least lower your chances of becoming a victim of card skimming listed in the order of most effective to least effective.
- Use your 'smartphone' to pay (Google Pay, Apple Pay) wherever you can. How to get this setup is outside of the scope but it is very easy. This is the strongest protection you get today, and it is extremely difficult (if not impossible) for criminals to scam you. Most POS devices accept these today although if you live in US (lagging behind the world) it is not uncommon to see vendors using ancient devices that does not support smartphone pay.
- Use 'chip+pin' if your card and the POS device supports, this is the second-best way. If you live outside of US like Europe, even in India, you are golden because it is the standard for POS devices for many years and you are required to use pin to do transaction. Every time I was on a business trip to India, I always find myself arguing with waiter at restaurants “hey, I don’t have a pin” 😄. If you live in US, it sucks since chip+pin is not mandated for whatever reason.
- Use 'chip' if your card and the POS device supports. Most credit card/banks these days issue cards with chip but unfortunately in US, they also include the magnetic strip to cover the lazy ass vendors who still use archaic magnetic swipe. This pretty much negates the benefit of chip as scamming devices can still read your magnetic strip. So, if you live in US, what I’d recommend is to scratch the magstripe on purpose (I did that on all my cards). Use a sharp knife or steel wool to scratch the magstripe to a point it can’t work. Keep one card with magstripe in case the vendor says, “we don’t have chip reader you have to swipe”. Trust me these guys won’t change unless they are mandated by law to switch to modern POS at state/federal level.
- Use ‘tap’ if the POS device and your card supports it. If you see this
 symbol on the back of your card, then it is enabled for RFID. Again, US lags on this protocol as well. While this is the most convenient way to make purchase, there is a huge security hole in this method which enables most sophisticated attacks which I won’t go into detail but there are things you can do to avoid them i.e., use an RFID blocker (you can buy them at amazon for $2 a piece) and place it in your wallet/purse along with your credit/debit card equipped with this technology. I use these if you need a recommendation https://link.selvansoft.com/1307688f
symbol on the back of your card, then it is enabled for RFID. Again, US lags on this protocol as well. While this is the most convenient way to make purchase, there is a huge security hole in this method which enables most sophisticated attacks which I won’t go into detail but there are things you can do to avoid them i.e., use an RFID blocker (you can buy them at amazon for $2 a piece) and place it in your wallet/purse along with your credit/debit card equipped with this technology. I use these if you need a recommendation https://link.selvansoft.com/1307688f - Use 'check' which of course has many problems of its own but it may be slightly better than the last one below.
- Lastly, if none of the above options available to you, you have no choice but to use magstripe/swipe. You might want to spend few seconds to look for signs of tampering on the POS device. See the picture at top of this blog for signs to look for. Obviously, you won’t have lot of time besides, you may annoy other customers behind you if you are spending too much time poking around the device 😄
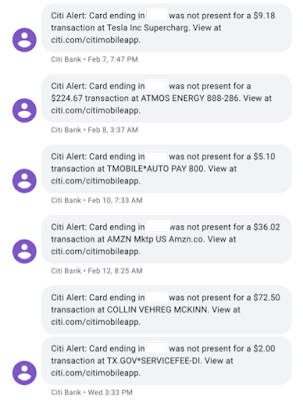
Finally, you can and should setup text alerts when your card is charged even for a $1. Almost all bank/credit card institutions provide the feature to TXT. The only annoying thing is getting TXT for everything you do on your card, but it is better than being a victim.
My text alerts look like this (see screenshot below). Notice it says “card ending in xxxx was not present” that has multiple meaning but, in this case, it means these transactions are done without card i.e., done with google pay which I use everywhere it is accepted and it’s the most secure way today to pay at POS. Period.
Here are some links on card skimming
Tuesday, May 23, 2023
ProtonVPN - fast & free
ProtonVPN
Not sure any of you are aware of Proton Mail which is a fully secure email service and has been around for a while. I signed up for their free tier email service a while back but never used it since I don’t want to pay for yet another cloud space and the free tier space of 500 MB is not much for daily use.
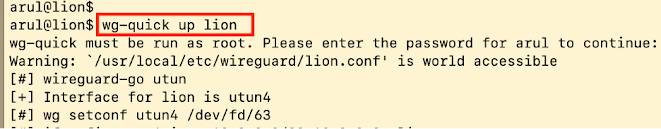
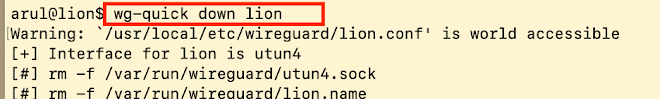
Anyway, I know they had VPN for free as well but never tried it until recently and I am blown away by the speed --- very low overhead compared to different VPN service I have used. Granted it is wireguard, a modern successor of VPN but still, literally I get same speed as provided by my ISP. First, I could not believe and started measuring speed with every speed test tool that is out there and they all came back with more or less same and speed which is roughly same as what I get with my ISP (see screenshot) without VPN layer. At this point, there is absolutely no reason to not use them permanently… and it's Free!
How to get ProtonVPN
Head out to https://proton.me and sign-up for free account and you get encrypted mail service and 1 VPN connection free. Wireguard is pretty simple to use, all you have to do is install wireguard (https://www.wireguard.com/install/ ) and get the credentials/keys from ProtonVPN and off you go.How to run wireguard (MacOS or Linux)
Wednesday, April 5, 2023
HOWTO: Credit Freeze
Data breach incidents are very common these days. In-spite of all the efforts & money spent by organizations on robust cyber security measures to protect themselves, data breaches continue to occur. With countless sensitive records compromised, it serves as a stark reminder that no organization or individual is immune to cyber threats and as an individual, there is nothing you can do to stop. However, there is one thing you can do to protect your identity and personal data by adding a credit freeze on demand or forever.
As a matter of fact, I don’t see a need for your credit report to be in “unlocked” status unless you apply for loan, bank account, credit card etc. which you don’t do every day. So, why does it need to be in “unlocked” status? When you need it, you can, with a click of a button (at most bureaus) unlock your credit, get your business done and lock it back.
I have listed below all you need (link/phone/address etc) to place a “free” (yes free) credit freeze to avoid becoming a victim of identity theft, fraud and scam that could potentially wipe your hard-earned money and ruin your financial reputation, possibly forever!
EQUIFAX:
By phone: 800-685-1111
By Mail: Equifax Security Freeze, P.O. Box 105788, Atlanta, Georgia 30348-5788
Online Account:
Terminology: FreezeHow To Lock: Home and select Freeze on the side barDirect URL: https://my.equifax.com/membercenter/#/freeze
EXPERIAN:
By phone: 888-397-3742
By Mail: Experian Security Freeze, P.O. Box 9554, Allen, TX 75013
Online Account:
Terminology: Security FreezeHow to Lock: Experian is sneaky & goes out of the way to hide the free service pushing customers to pay for the “File Lock” (a paid service). Use the direct link below to get to the ‘free’ option.Direct URL: https://usa.experian.com/member/security-freeze
TRANSUNION:
By Phone: 888-909-8872
By Mail: TransUnion LLC, P.O. Box 2000 Chester, PA 19016
Online Account:
Terminology: Credit LockHow To Lock: Dashboard has Lock/unlock buttonDirect URL: N/A
INNOVIS:
By Phone: 866-712-4546
N/A
Final Note: The information above is designed to be simple and easy to follow, so that anyone can place a credit freeze quickly and easily. Permanently freezing your credit reports is sufficient in protecting yourself from identity theft. However, I did encounter a more complex process outlined on Reddit (link below) that focuses on all the steps to take if you were indeed an identity theft victim. Some of the steps mentioned there are very extreme and complex, but I suppose overprotecting yourself isn't bad, especially when it comes to your identity.
Stay Informed and Safe Online
Saturday, March 18, 2023
ChatGPT vs. Google search
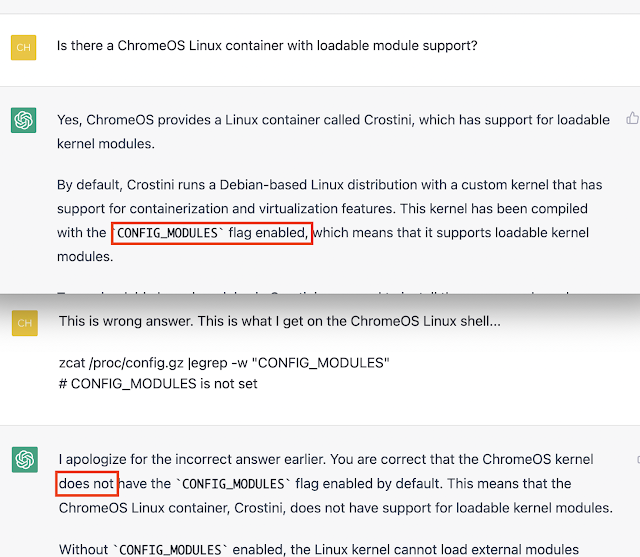
Ever since ChatGPT came along, I find myself going there in the hope that I will find what I am looking for faster and easier using the conversational search approach. However, I often find myself falling back to Google search because 4 out of 5 times ChatGPT gives me wrong information and directing me in the wrong path (see the screenshot at end). At this point, I am convinced that it is actually faster for me to go to Google search in the first place for accurate information. Granted my search needs are highly technical in nature and I understand that is not exactly same for everyone but still I think Google search is faster, and most importantly accurate, at least for now.
What do you think?
Just for fun, I asked ChatGPT the question and here is the response I got.
“When it comes to finding specific information quickly, Google search is still the go-to tool for most people. However, if you want a more conversational and personalized response to your query, ChatGPT can be a great option.”
Here is a screenshot of one of the flat-out wrong answer from ChatGPT for one of my search/question with high degree of confidence 😆
Tuesday, March 14, 2023
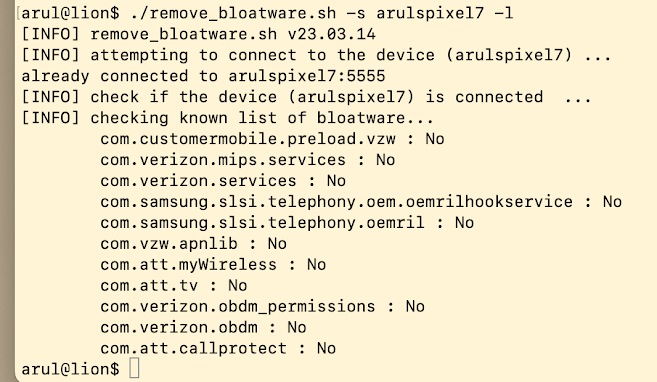
Bloatware in Pixel?
I only buy Google Pixel phones to avoid carrier & phone manufacturer installed, un-removable bloatware but little that I know these bloat kings like Samsung, Verizon, AT&T, etc managed to shove their crap on my Pixel phone and I have no clue how they managed to do that. I accidentally discovered some and believe it or not, you can't remove it without ‘root’ing your phone which will disable monthly security patches. Long story short, I wrote a script to disable them from running.
Feel free to use this script but you need to have android adb installed on your computer and connected your phone with USB cable in order for this script to work.
https://github.com/aselvan/scripts/blob/master/andriod/remove_bloatware.sh
If your phone is not pixel, you will find crap ton of bloatware. If you give me the full list (i.e., run my script '-a' option), I can update the bloatware list in the script so you can remove them. Right now, the list I have hardcoded in this script only includes what I found on my pixel which are listed below.
Tuesday, March 7, 2023
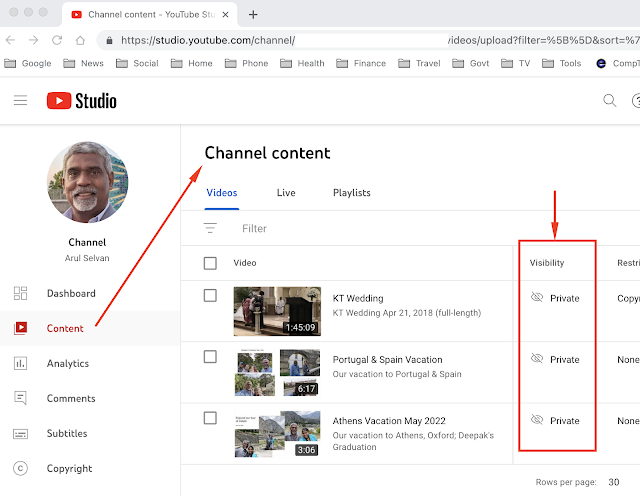
Free Cloud storage
Friday, March 3, 2023
Phishing scams using URL Shorteners
I am sure many of you are familiar with shortened URLs that redirect you to a different long-winded URL when clicked. If you’ve ever seen or used tinyurl.com, or a bit.ly link, you are already familiar with how they work.
These shorturl services like bit.ly etc., have been abused by scammers for their phishing campaign for a while now. Recently, there is an increased use of these technique specifically leveraging reputable/legitimate websites like linkedin.com (see link below) since malware protection software and spam blockers are unlikely to block these short links created by reputable organizations like LinkedIn.
So how do you know if your given short URL is not going to take you to a shady phishing site or worse, to a malware laced website? Essentially, what you need is an inverse of shorturl i.e., longurl 😁 which expands the shorturl to show where it would take you if you were to click. That is exactly what I have done on this simple tool below. Feel free to use.
https://selvansoft.com/longurl/
Note: Try expanding this sample short link (https://bit.ly/3YuGbTA) using the longurl service above. For safety, the redirect address is checked w/ out actually traversing there and also it goes just one level deep only. There is also urlscan.io that does lot more if you want to try that as well.
PS: I also have a very simple shorturl service similar to bit.ly here https://selvansoft.com/shorturl/ Again, feel free to use.
Thursday, January 26, 2023
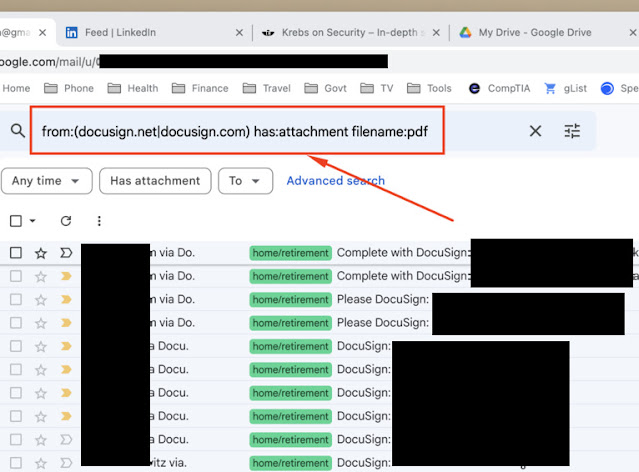
DocuSign sends sensitive info in plain text
Yes, you read the title correctly. DocuSign indeed sends everything including sensitive information to you after you complete "docusigning" something.
Have you ever used the DocuSign service for signing any documents? I am sure many of you are familiar with DocuSign because it is used very widely everywhere for document signing online. If you think you haven't used it, think again, you may have used it and not know about it. Typically, a lot of information you enter when you sign any legal document like your loan application, lease contract, loan, even job acceptance these days goes via DocuSign. When both parties completed the signing process, DocuSign will send you a mail with a copy of the fully signed/executed document (PDF file) once. The PDF file may likely contain your SSN, DOB, address, phone number, account number and many other sensitive information you may have entered during the signing process. Guess what, all of these are in "plain" form and sitting in your email (gmail, yahoo etc). If you don't believe me, search your email from docusign.net and open the attachment they sent you. You would not believe what you see.
If you use gmail (who doesn't?) here is a easy search filter to quickly show all mails from docusign containing PDF files.
"from:(docusign.net|docusign.com) has:attachment filename:pdf"
The screenshot below will help if you don't know how to search for e-mail messages with filter.
How to spot phishing attempt - an anatomy of a phishing Email
Note: This is an old post from 2014 at blog.selvans.net. It is moved to this site as part of migration. Though it is more than 8 years old, it is still valid and relevant.
If you consider yourself as someone who knows how to spot spam and phishing emails, you won't learn anything new here. Others who want to learn how to spot spam or phishing mails, especially if you are someone who simply can't resist clicking on links in your email no matter how many times you were told not to :) read on …
Like most of you, every now and then I do get a phishing mail delivered to my inbox. Gmail usually does a pretty good job of filtering spam and phishing mails, however, this particular one shown here slipped through gmail spam filter because of my own filter (a discussion on why it slipped is outside the scope of this blog). Anyway, here is a screenshot of the phishing mail we will be dissecting in this blog. Apparently, citibank all of a sudden lost everything they know about me except my email address :). You can stop right here since it is clearly a phishing attempt, but for the purpose of this exercise, lets continue. At a glance, for a novice email user, it looks legitimate and it does appear to have come from citibank.com, and is instructing me to download the attachment called Citibank.html. It must be important since it is from citibank alert service and I should immediately download the file and double click it right? The first thing you need to understand is that the 'mail from' (i.e. in this case alerts@citibank.com) is the easiest thing to fake. To find out where it really came from you need to see the full email headers from the “show original” option. [Note: The screen shot below is from gmail but as far as I know all mail clients like yahoo, hotmail, outlook etc allow you to view the 'raw' content of the mail which will show all mail headers].Now, we are going to examine the attachment the crook wants you to download so he can collect your information. Typically, you can view the raw mail safely with your browser to see what the attachment contains to make sense out of it as long as its not binary. In this case it is supposed to be a HTML file. However, the crook encoded the content of the HTML text to base64 encoding so it is not easy to view what he is trying to do and where he intend to send your information (see the screen shot below).
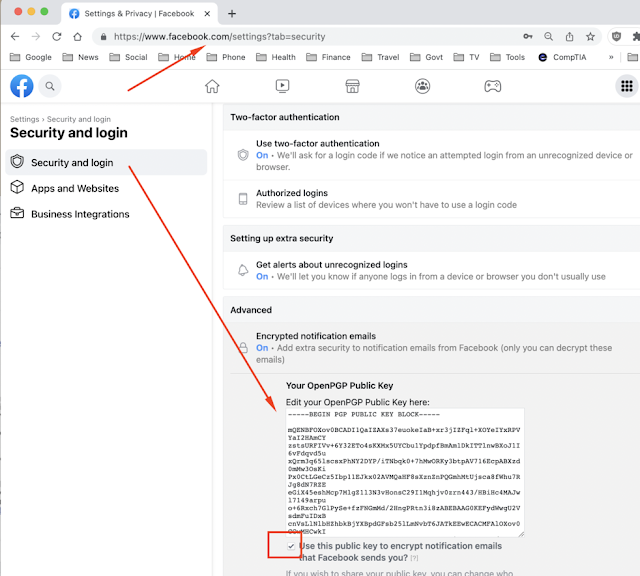
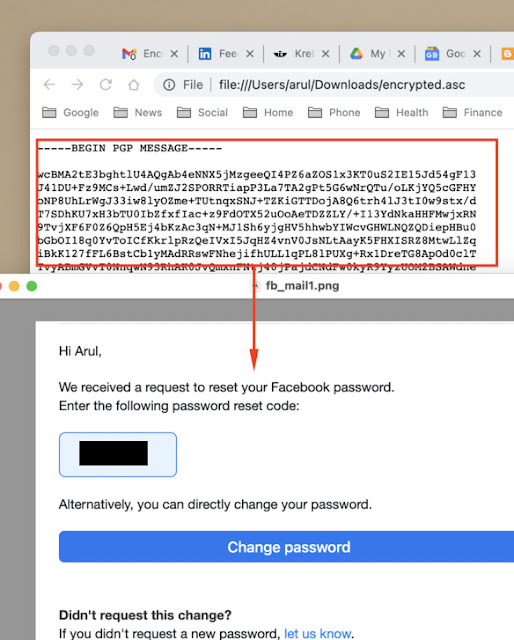
How to protect your Facebook account with encrypted notifications
Note: This is an old post from 2015 at blog.selvans.net. It is moved to this site with updated screenshot and content. Though it is more than 7 years old, it is still valid & Facebook still supports this feature.